By: Tom Hilton | Posted: May 13, 2020 | Updated: April 5, 2023
This segment of “My Internet enabled Life” talks about the evolution of the Internet and a bit about how it works.
I’m 73, and have been using computers and digital calculators since 1968. Check out the section I wrote on my History with Computers.
Before the Internet: ARPANET & Mainframes
Before the Internet, there was the Defense Department’s Advanced Research Projects Agency Network (ARPANET). ARPANET was developed as a way to share research data among Defense Department researchers, many of whom were university professors.
Back then data were entered into computers via IBM punch cards. The cards fed into a “card reader” that converted the punches to a series of zeros and ones which form the basis for digital processing that makes computers and the Internet work. Over time, punch cards were overtaken by digital bits entered into the computer operating system via keyboard and typed out on a wide roll of paper via a dot-matrix printer called a Decwriter so you could see what you were typing.

Caption: Mainframe computer and terminal
During the 1970’s, universities found ARPANET to be increasingly useful. Programmers too realized that you could share technical reports and not just data. This need sowed the seeds for email.
The actual world-wide-web (WWW), now called the Internet, was not possible until 1973 with the invention of the Transmission Control Protocol/Internet Protocol (TCP/IP) which went out and found every live network and linked them together. That led to the need for an address system, the new Domain Naming System (DNS). However, what really enabled email was the creation of the Simple Mail Transfer Protocol (SMTP). After that, reliable email exchange became a snap.
Why all the acronyms? Because eventually, you will see this alphabet soup and not be confused by it.
A Side Note on PCs
Coincident with the evolution from the ARPANET to the Internet, black and white monitors (sometimes green and yellow) replaced the noisy and cumbersome punch cards and dot-matrix printers. As television technology advanced, so did monitors.
Perhaps the biggest evolutionary event was the advent of the personal computer work station which used a TV-type monitor placed atop a briefcase-sized computer on one’s desk (ergo the term desktop computer).
Several companies introduced PCs to the marketplace including IBM, Tandy, Dell, and Apple. However, it was the 1986 mass-produced Zenith model Z-240 series that almost overnight gave birth to the modern PC that sits in your home today. Zenith landed a huge contract with the Federal Government. Soon Zenith PCs were on office desktops all across the country. Within a year, the design of the Z-240s was adopted by most competitors and prices started dropping while features started improving.
PCs quickly provided a powerful replacement for electric typewriters because a) there was no need for correction fluid or erasers to make corrections, and b) they could send what was typed directly to the recipient over the Internet via email – even if it was to your boss in the next office.
So, you see, there has long been a mutual interdependence between computers and the Internet. You cannot have one without the other.
ARPANET to BITNET to the INTERNET
Between 1973 and 1985, while the Internet and email were evolving, a number of ARPANET alternative networks popped up on the WWW, mostly among science labs and federal science agencies like the National Science Foundation (NSFnet). However, home use was nearly impossible back in the early days, because until the 1980s, computers were too huge to fit into one’s garage much less office.
The main motivation for developing alternatives to ARPANET was to skirt DOD limits on usage. Perhaps the most popular university network that evolved was known as Because It’s There NET (BITNET). BITNET saw a linear increase in use during the 1980’s, and that popularity increased civilian dependence on computers and their networks just as computers started shrinking in size.
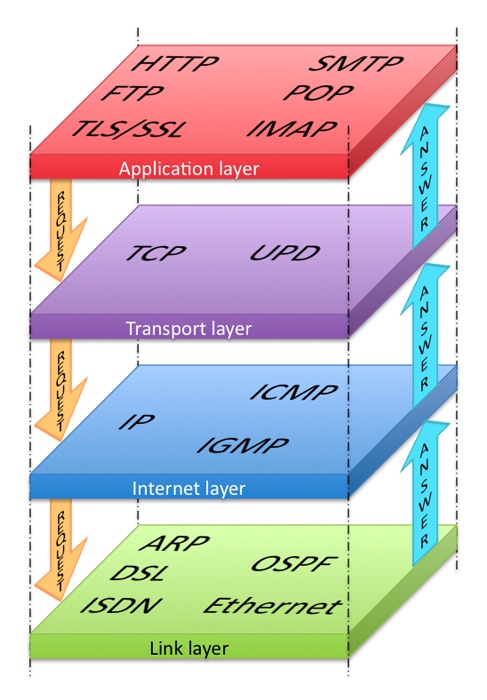 By the early 1990s, the modern Internet emerged with the help of yet another acronym – the Hypertext Transfer Protocol (HTTP). What HTTP did was allow users to use TCP/IP to search for and access archives of stuff just sitting around on the world’s hard drives like a dusty library. HTTP made it easier to scour the Internet to locate not just email inbox addresses, but documents and various information services provided by libraries and the popular online Wikipedia encyclopedia.
By the early 1990s, the modern Internet emerged with the help of yet another acronym – the Hypertext Transfer Protocol (HTTP). What HTTP did was allow users to use TCP/IP to search for and access archives of stuff just sitting around on the world’s hard drives like a dusty library. HTTP made it easier to scour the Internet to locate not just email inbox addresses, but documents and various information services provided by libraries and the popular online Wikipedia encyclopedia.
That is why today when you search the Internet for information, the result comes back “http://” followed by “www” followed by the Domain Naming System (DNS) address. Today, most browsers automatically send “http://” and the “www”. when you enter the website address – like techenhancedlife.com
Browsers
The first popular commercial plain-language Internet search engine that allowed users to “browse” or “surf” the Internet was introduced to the market in 1995 by Microsoft as the Internet Explorer (IE) browser. The term “browser” caught on because Internet users were, in effect, using HTTP to browse for information. IE became very popular because Microsoft distributed IE with its market-dominant operating system, Windows. It even dominated the Federal government – until – 1998 when Google launched a competing search engine.

There were a variety of Internet service providers (ISPs) who offered email (AOL and Comcast for example), and there were, and still are, browser options to Google and IE such as Firefox, Edge, and Safari to name a few.
Google quickly wound up dominating the browser market because it was faster than IE and other less-popular browsers at finding answers to people’s search questions.
Google used search algorithms that dredged up more useful information by tracking the search history of international web users to produce results ordered by user popularity. For example, if when people searched for hamburger restaurants, and McDonalds was the site opened most often selected, results would start with McDonalds, then maybe next would be Burger King, In-N-Out Burgers, etc.
Today, Google’s Chrome browser continues to evolve so that searches take into consideration such things your physical location and your own past search history. Thus, if the nearest McDonalds is 10 miles away, your top results might be Burger King and Five Guys because they are only a few miles away.
Google’s success encouraged a number of new browsers seeking niche users, notably Firefox and Apple’s Safari which, like MS IE (now Edge or Bing), comes with the Apple PC operating system. Microsoft tried to win users back with a new browser called Edge but it had little impact on Google use.
Google also morphed into Chrome which offers its users significant ability for modifying how it functions in order to improve the fit with personal needs. For example, I live in Eastern Europe part of the year, and some of my US banks will block access to my accounts from Bulgaria. However, I have a browser extension app that lies about my TCP/IP so US gateways think I am browsing from the UK or the Netherlands – and let me log in. Another tool lets me switch to encryption when banking online. Finally, Google offers online software options to Microsoft’s PC-based Office suite of programs, for word processing, spreadsheets, and graphics.
I would be remiss in talking about the Internet if I did not at least mention smartphones. Most smartphones today allow owners to surf (browse) the Internet remotely via radio waves. iPhones use Safari, and Android phones use Google (which owns the Android operating system). Smartphones popularized the term “App,” which is short for application – small programs that can be downloaded to your phone to enable word processing, email, calculations, maps, etc.
The term “App” has become synonymous with small programs that offer useful niche tools for users. One of my favorites is Grammarly, a free tool that helps me catch typos and punctos when writing emails, comments, and web content like this in my browser.
The INTERNET Jungle
Finally, I have to warn readers that the world wide web can be a dangerous place. The Internet is full of crooks, charlatans, thieves (called hackers), extortionists, and even kidnappers (of your PC data).
The best protection is to pay a quality Security service to protect you from “viruses” that can delete your data or steal your passwords, or otherwise just vandalize your computer software, and “malware” which masquerades as innocent software you naively download or that sneaks in your back door while downloading an app, photo, or file – then spies on you, or otherwise corrupts your computer.
There are a number of services that combine anti-virus and anti-malware protection as well as protect you from things we do not even know are lurking out there on the web. Kaspersky, McAfee, and Bitdefender are highly trusted. They offer family packages that even include smartphone protection and things like virtual private network (VPN) services which encrypts what you send over the internet to brokerages, banks, online retailers, and of course, secret messages between spies. VPN internet exchanges cannot be hacked – read or corrupted by evil-doers.
Is it worth it? For peace of mind alone, yes!
Imagine if all your passwords were stolen. I have over 100 of the darned things. How long would it take to change every password to every bank, retailer, email service, website, etc.? Then add to that the hassle of convincing your credit card company that you did not buy $2,000 worth of wine online or withdraw $10,000 from your checking account.
Later, I will offer you a simple method for storing your passwords on a word document that only you can make sense of and/or your MS Outlook or Google contacts list.
*Disclosure: The research and opinions in this article are those of the author, and may or may not reflect the official views of Tech-enhanced Life.
If you use the links on this website when you buy products we write about, we may earn commissions from qualifying purchases as an Amazon Associate or other affiliate program participant. This does not affect the price you pay. We use the (modest) income to help fund our research.
In some cases, when we evaluate products and services, we ask the vendor to loan us the products we review (so we don’t need to buy them). Beyond the above, Tech-enhanced Life has no financial interest in any products or services discussed here, and this article is not sponsored by the vendor or any third party. See How we Fund our Work.

