By: Bob Glicksman | Posted: August 23, 2016 | Updated: May 8, 2025
Introduction, from the editor: Using a handful of simple, non-intrusive sensors, retired engineer Bob Glicksman has been able to learn all sorts of important things about the daily routine of an elderly person, who has cognitive impairment, and for whom he cares. He has been able to make multiple successful interventions to stave off what might have otherwise been serious adverse events.
In fact, this simple sensor setup has worked better than he expected. Below Bob (the author) shares his experiences, as an example of a real world use case in which a small addition of technology can accomplish a lot.
Few Sensors, Lots of Information: Excellent Results.
The author found that a passive sensor home monitoring system can provide a surprising amount of information about the ability of an elderly person to be safe in their home and to perform the routine activities of daily living.
This finding is thought to be important as there is the perception that a useful sensor system must be complex, extensive, and unduly invasive of privacy. Alternatively, there may be a perception that simple, relatively non-invasive sensor systems cannot supply sufficient information to be useful. This study shows that both perceptions may be false.
The goal of a passive sensor home monitoring system is to provide remote caregivers with sufficient information about an elderly person’s daily activities and routine in order to:
- Assess the elderly person’s overall state of mental and physical health, on a near real-time basis, so as to flag instances when some intervention may be needed (e.g. ascertain if the person is getting out of bed and eating meals);
- Provide sufficient insight into an elderly person’s normal daily routines in order to raise “red flags” about significant changes to the routine that may indicate a change in the caregiving needs or suitability of the living environment; and
- Ultimately, provide evidence that the elderly person is no longer safe in their current living situation and information to guide caregiver decisions about changes that need to be made (hopefully, before the elderly person’s health or wellbeing is impacted).
The e-book “Caring from Afar [1]” provides a wealth of information about commercially available systems as well as criteria and analysis to aid in system selection.
About Me and “The Subject”
The author is the caregiver for a subject who resides in an independent living facility. The subject is over 100 years old, but is physically able to perform the routine activities of daily living. Notwithstanding this, the subject suffers from severe short term memory loss, dizzy spells, and occasional confusion about where she should be and what she should be doing.
The caregiver normally checks in on the subject by telephone, at least twice a day. The subject does not use a mobile phone, so these telephone checks must be performed when the subject is in her apartment. The caregiver has long been troubled by the lack of information about when the subject is at home. For example, the subject’s usual pattern is to get up, get dressed, and leave her apartment for breakfast in the communal dining room at approximately 7 am each morning. A good time for the caregiver to telephone the subject is just before she leaves for breakfast. However, there are times when the subject does not answer the telephone leaving the caregiver with a dilemma – is the subject simply a little early and has already left for breakfast or has the subject fallen and unable to get up to answer the phone? What should the caregiver do about this?
Motivated by such questions, the author considered installing a commercial monitoring system. However, these systems are relatively expensive and the author was unsure if any system could answer these questions. Given this, the author, along with co-developer Jim Schrempp, developed a simple home monitoring system called “SIS [2]” (see Appendix A). While this paper presents results based on SIS data, the conclusions will equally apply to commercially available systems.
Installation in the Subject’s Apartment.
The original objective of this installation was to provide the caregiver with information about when the subject is home and away from home. Consequently, only two sensors were installed in the subject’s apartment, as depicted in figure 2:
- A magnetic separation sensor over the front door; and
- A motion sensor on the wall near the front door.
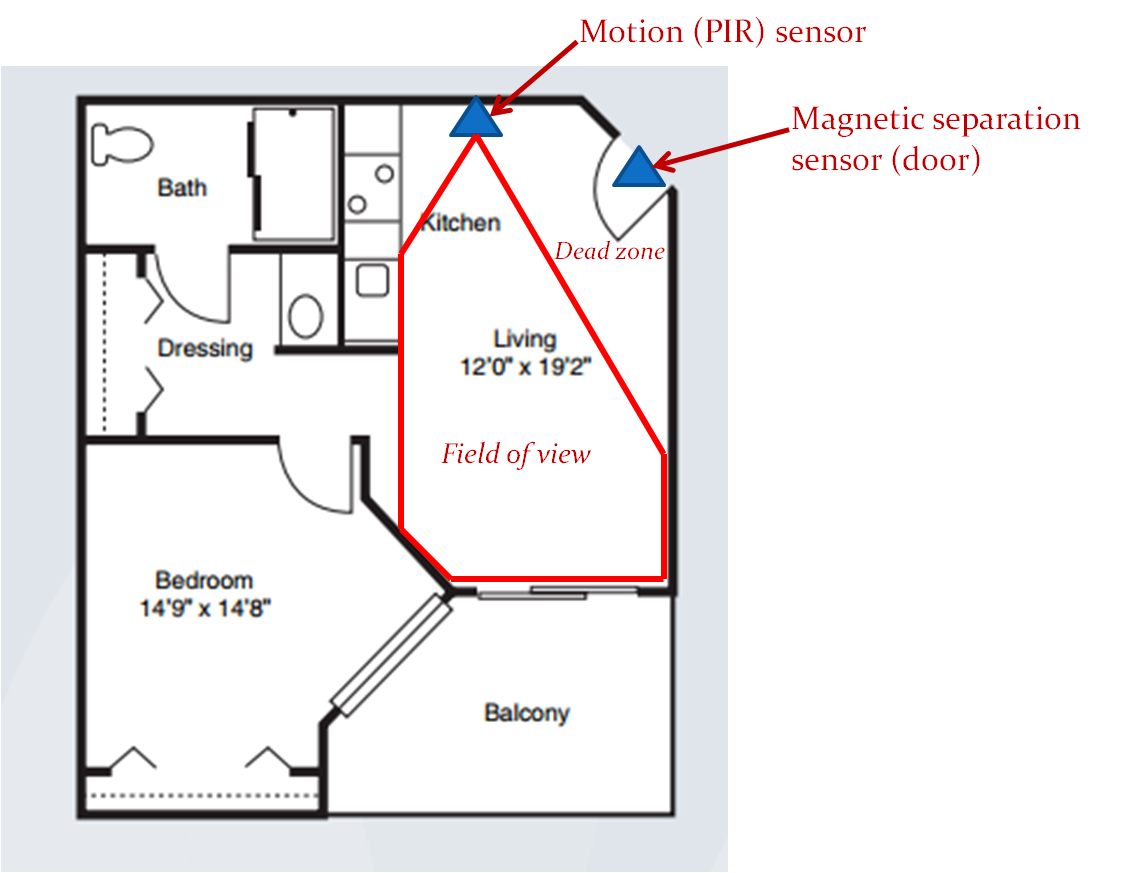
Figure 2. Sensor Placement.
The motion sensor is placed so that it covers most of the “great room” that must be traversed when entering or exiting the apartment. The motion sensor is aimed so as to create a dead zone just in front of the door. This was done to ensure that the motion sensor is not inadvertently tripped by the opening or closing the door. This sensor placement supports a simple set of inferences about the subject’s whereabouts:
- If the door sensor is tripped and then the motion sensor is tripped, a person must have entered the apartment. If the subject is alone, then the subject must be at home.
- If the motion sensor is tripped and then the door sensor is tripped, and if no sensors are tripped for 10 minutes thereafter, the subject must have left the apartment and is therefore away from home.
These sensor “events” and “inferences” are time-stamped and recorded in the SIS log. The caregiver can read out the log contents remotely, at any time.
Sensor Log Interpretations.
Experience with this simple SIS installation in the subject’s apartment has provided the caregiver with significant and unexpected insight into the subject’s activities. This is because the subject’s location says some things about what they are doing. In an independent living situation, “at home” activities include:
- Sleeping
- Dressing
- Personal Hygiene
- Quiet recreation (reading, watching TV, etc.)
Conversely, “away from home” activities include:
- Eating meals
- Socialization
- Participation in group activities.
A simple, 2-sensor system cannot provide further insight into the subject’s activities within each of these groupings, but some reasonable inferences are still possible. For example, since meals are served only during certain time periods, the subject is probably eating the meal if she is “away from home” during one of these periods. More certainly, the subject is not eating if she is “at home” during a meal period. It is possible, or course, that the subject may be eating inside the apartment at this time, but if the subject’s normal pattern is to eat meals in the communal dining room, then the fact that the subject is at home when a meal is being served is at least a “red flag” that something unusual is happening. While the simple 2 sensor system cannot provide more information about this situation, the caregiver can use the “red flag” to trigger some other form of follow-up investigation, e.g. a telephone call to see if the subject is OK.
Specific Sensor Log Examples.
A few examples of extracts from the SIS sensor logs illustrate how inferences about a subject’s activities can be made and how “red flags” can be raised. SIS provides two views of the sensor data log: a graphical view and a detailed textual readout of the log.
Figure 3 contains a screenshot from one 12 hour graphical display of the SIS log in the subject’s house. Figure 3 has been annotated to clearly show relevant time periods during the day.
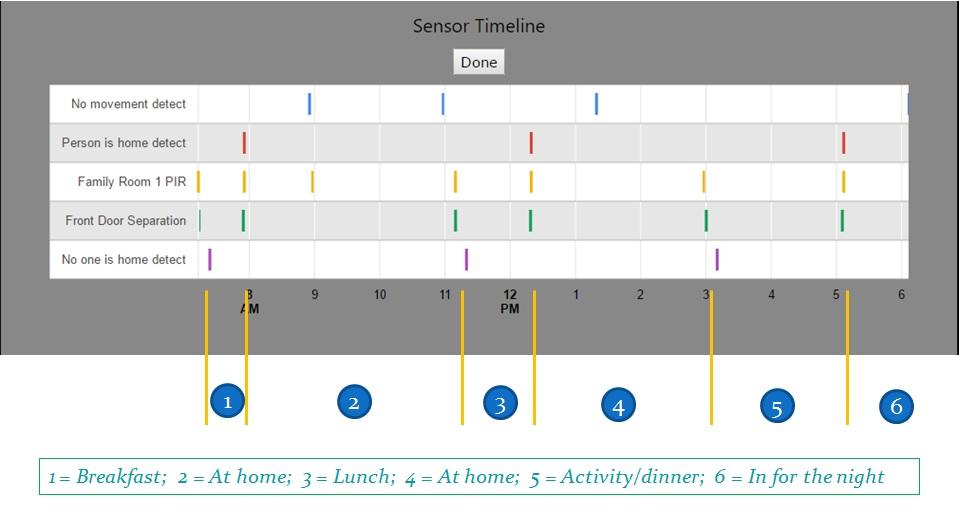
Figure 3. Graphical Display of a “Normal Day”.
Referring to figure 3, “events” from the two sensors (Front Door Separation and Family Room 1 PIR) are displayed on a timeline, along with three “inferences” made from these sensor events (No one is home detect, Person is home detect, and No movement detect). The subject’s location is easily seen by paring the No one is home detect and the Person is home detect inferences on the timeline. Please recall that No one is home detect is logged if the Family Room 1 PIR is quiet for 10 minutes after the front door sensor trip. Therefore, the time stamp for No one is home detect is 10 minutes later than the actual exit event.
The inference No movement detect is drawn by SIS whenever the person is at home but no sensor is tripped within a one hour period. It must be noted that since there are no sensors in the private areas of the apartment or on the balcony, the fact that no sensor is tripped does not mean that the subject is not in motion – only that she is not in motion in the Great Room or opening the front door.
Referring to figure 3, period (1) shows that the subject is out of the apartment from approximately 7 am until shortly before 8 am. This is consistent with the subject going to breakfast, as this is within the time period that breakfast is served in the dining room of the facility. It is therefore reasonable to assume that the subject ate breakfast and returned to her apartment afterward.
The subject was at home during period (2), i.e. between about 8 am and shortly after 11 am. There are several No movement detect inferences during this time period: one at about 9 am and a second about 11 am. Since these inferences are spaced more than one hour apart, there was some Living Room PIR trip event(s) within this period of time. In fact, it is clear that a family room PIR sensor trip event happened at just about 9 am. So the subject was in the back of the apartment between 8 and 9 am but came into the Great Room at about 9 am and was moving through there at least periodically over the next hour. From 10 am to 11 am, the subject was in the back of the apartment because another No movement detect inference was made around 11 am. The subject left the apartment at about 11 am. It cannot be determined exactly what the subject was doing during these No movement detect periods of time. She may have been sleeping, resting in bed (watching TV or reading), or bathing. However, it can be determined that she was not socializing, as she was clearly inside her apartment.
The subject was out of her apartment during time period (3); between a little after 11 am and about 12:15 pm. This is consistent with the subject going to lunch, as this is within the time period that lunch is served in the dining room of the facility. It is therefore reasonable to assume that the subject ate lunch and returned to her apartment afterward. The subject was in her apartment during period (4); i.e. from about 12:15 pm to about 3 pm, after which she left during period (5), between about 3 pm and a little after 5 pm. She returned to her apartment after 5 pm and was inside for the rest of the evening and night: period (6).
There is a No movement detect inference at about 1:15 pm during period (4), so the subject was in the back area of her apartment during this time. There are no Family Room PIR trips until she leaves at about 3 pm, so she was either washing, sleeping or performing quiet activity in the bedroom all during period (4).
Period (5) begins about 3 pm, which is before dinner (first seating at 4:15 pm). Consequently, the subject was likely socializing outside her apartment until dinner time. She returns to her apartment a little after 5 pm and since she is scheduled for the 4:15 dinner seating, it can be assumed that she ate dinner as well.
The overall pattern of figure 3 is within the constraints for a “normal” day. The subject obviously got up in the morning, got out of bed, got dressed (she won’t leave the apartment without being dressed) and went out (presumably to breakfast). She also went out at lunch time and was out during dinner time, so she likely ate all three main meals. She spent a lot of time quietly inside of her apartment but she also was out during a socialization period. Therefore, no “red flags” are raised on this day. The subject was performing routine activities at the expected time periods, and this is what is important for the caregiver to know.
Figure 4 contains some samples of the textual readout of the SIS Log from a different period of time than Figure 3. The textual log readout makes it easier to see the precise time of logged events and inferences. Over on the left hand side of figure 4, we can see a sample of the log from about 7:30 am to about 8:13 am on the date 5/3/2016. It is interesting to note that the subject left her apartment at 7:38 am and returned at 8:11 am, a total time away of 33 minutes. It is reasonable to assume that she went to breakfast at this time. Now, the transit time from the subject’s apartment to the facility dining room is about 5 – 10 minutes [3]. This transit time is incurred twice; once going and once returning. The average total transit time is therefore about 15 minutes. Consequently, the subject spent no more than 18 minutes in the dining room.
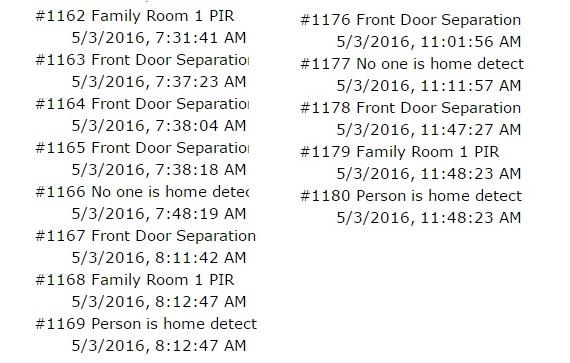
Figure 4. Meal time excerpts from the Log.
The facility dining room is a sit down affair with servers taking the meal order and serving the meals to the residents. So what might an 18 minute meal time infer? How much time might be spent in discussing meal options with the server and with the server ordering/preparing, assembling and serving the meal? How much time is left to consume the meal? These questions lead to some possibly troubling conclusions: either the subject spent some time ordering and little time eating, or the subject is known to order the same meal choice every breakfast, so the servers can serve her immediately, leaving a full 15 or so minutes to eat. Either way, this short period of time raises a “red flag” about the quantity and/or variety of the subject’s meal choices.
The right side of figure 4 shows a sample of the log from about 11:01 am to 11:47 am the same day. This would be lunch time, and given the times in the log, the subject could not have spent more than about ½ hour ordering and eating lunch. The same logic applies here as for breakfast: is the subject ordering the same meal choice every day?
Obviously, a snapshot of one day does not, in itself, mean very much. However, this is an example of the kind of “red flags” that a simple, small sensor system can provide, even when there are no sensors at all in any place that is associated with serving or eating meals. Certainly, if the caregiver notes a sudden and repeated change in the subject’s eating habits, a “red flag” can be raised, indicating that further investigation is warranted.
Figure 5 contains a snapshot of the textual log readout at a different time of day.
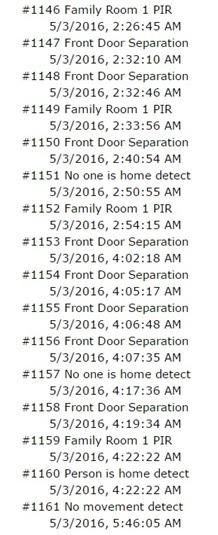
Figure 5. Wandering at Night.
Note the times logged in figure 5. This is the middle of the night! On this night, the subject was up at about 2:30 am and opened the front door several times before finally leaving her apartment (at 2:40 am). She returned to her apartment at 2:54 am, about 15 minutes later. Recall that 15 minutes is the nominal round trip transit time between the subject’s apartment and the common areas of the independent living facility. The subject obviously was confused! Not only did she open the front door several times before exiting (indicating that she was likely confused about the time and what she was going out for), but she returned in the “minimal transit time”, indicating that she probably went downstairs and then realized that it was not socialization time nor mealtime when she found that the facility was quiet and nobody was around [4]. A similar pattern repeated about 4 am that same day.
This is a clear “red flag”. The subject perhaps had insomnia, was confused about the time of day (possibly mixing up day and night), and it clearly indicates that the caregiver should check in with her the next morning to ensure that she is OK. This check-in was done and the caregiver was able to get the subject back on a normal schedule.
Interventions.
The terms “red flag” and “remote interventions” have been mentioned several times in this paper. One finding from this installation has been that “red flags” arising from a very simple passive sensor monitoring system can indeed trigger telephone interventions that are significant in giving the caregiver a level of comfort about leaving the subject in her present independent living situation [5]. Two anecdotes will serve to illustrate this point.
Day/Night Mix Up.
The caregiver reached the subject by telephone at 7 am on one particular day, after the sensor log data established that she was at home. The subject answered the telephone by announcing that she was going to bed and wished the caregiver goodnight. The caregiver noted activity in and out of the subject’s apartment several times during the previous night (from the sensor log, similar to that discussed in the previous section). On this basis, the caregiver decided to let the subject nap for an hour or so. The caregiver called back at a little past 8 am and was again answered by “goodnight, I’m going to sleep”. At this point, the caregiver intervened and made the subject realize that it was 8 in the morning and not 8 at night. After talking though this confusion several times, the subject got the point and agreed to get up and go eat breakfast. Sensor log information showed that the subject was back on a normal schedule from that point on.
Missed meals:
The caregiver used the SIS interface to check on the subject’s whereabouts close to her scheduled dinner seating time found that she was in her apartment. The caregiver called and actually awakened the subject. The caregiver reminded her that this was her dinner time, whereupon the subject agreed to get up, wash, and go to eat dinner. The caregiver checked the sensor log again about ½ hour later and found that the subject was still at home. The caregiver called again and the subject again promised to go and eat dinner. The caregiver checked the sensor logs once more about 20 minutes later and again called the subject when it was determined that she was still at home. This time, when the subject insisted that she was going to eat dinner, the caregiver intervened saying “you must be tired and you really don’t feel up to going to eat dinner – right?” The subject agreed, at which point the caregiver offered to order dinner to be sent up to the subject’s apartment [6]. The caregiver checked the logs later and found a pattern indicating that dinner had been delivered. The caregiver called the subject in the evening and verified that the subject did receive dinner and had eaten.
Taken in isolation, the “red flags” triggering these incidents might simply be indications that the subject was not feeling well that day. When it was noted that these sorts of things had become a consistent pattern over time, there was concern over the subject’s ability to continue in independent living. Nutrition and socialization were both in jeopardy, arising from an overall decline in the subject’s ability to deal with time. However, with “red flag” information from the sensor system triggering remote telephone interventions, the caregiver (and family) believes that the situation is manageable and that it is safe to leave the subject in independent living, at least for the time being. This finding supports the overall premise of passive sensor home monitoring systems – that such systems can help a person remain in their current living situation longer than it would be otherwise prudent for them to do so.
Summary and Conclusions.
Experience with a simple passive sensor home monitoring system has demonstrated that a wealth of information is available with very few sensors, including no sensors in private areas of the home. In an independent living facility, a system consisting of only 2 sensors has demonstrated the ability to raise “red flags” to which a caregiver can respond, often with a simple telephone call. The combination of “red flags” and the follow up remote interventions have further demonstrated that a passive sensor home monitoring system can indeed allow an elderly person to remain in their current living situation when it would otherwise be unwise or unsafe for them to do so.
The author believes that these results can be expanded beyond independent living to a person living alone in a house or apartment. Depending upon the home’s physical layout, similar results might be obtained with only one or two additional motion sensors, also in non-private areas of the home. The author hopes that this will soon be tested and validated. Smaller sensor systems are less invasive to personal privacy than are large, “whole home” systems, and reduction in sensor information may not be as significant to the overall goal of keeping an elderly person safe in their home as might have previously been assumed.
Appendix A. Background on the SIS system
This section provides a high level overview of the SIS system. SIS uses very inexpensive wireless alarm-system-type sensors to provide information about a person’s activity in their residence. Figure 1 depicts the architecture of SIS.
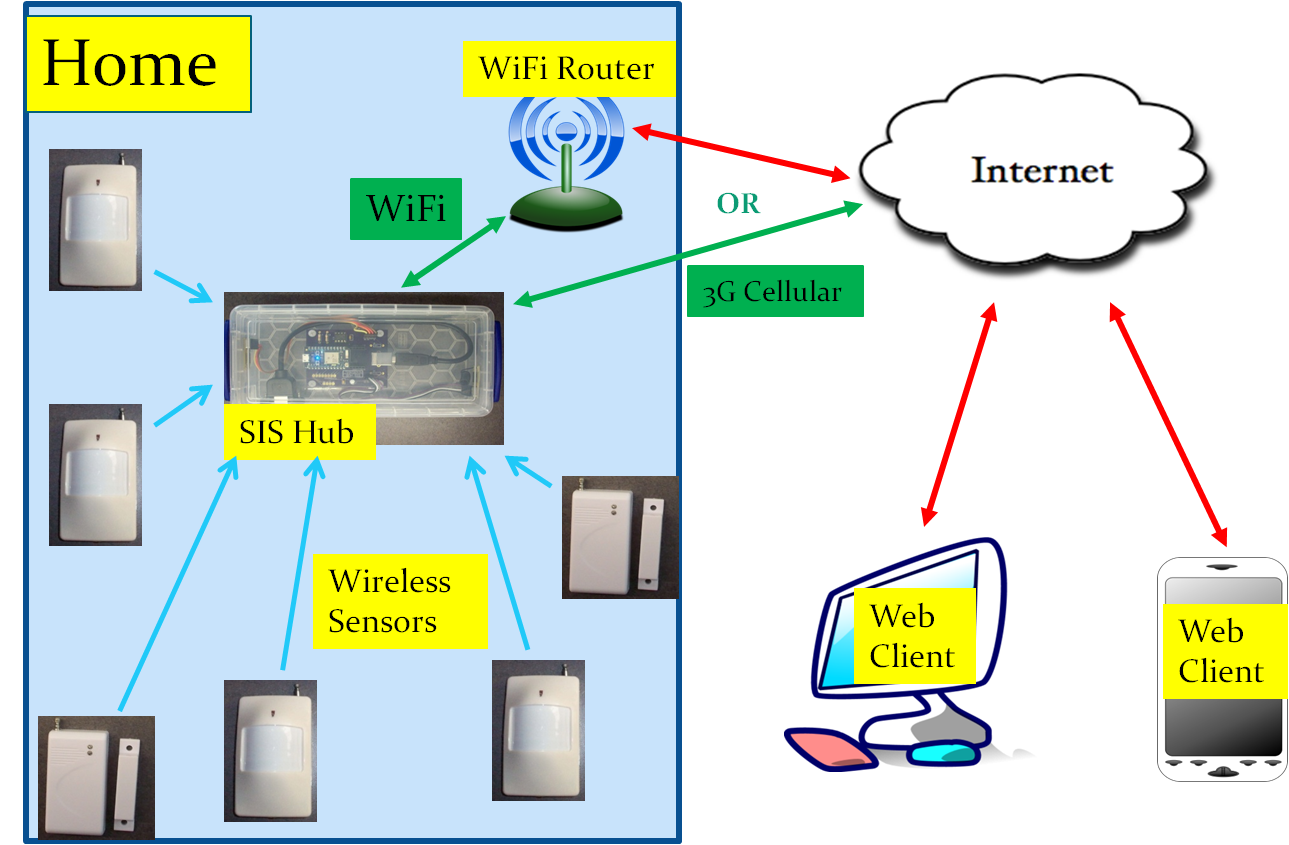
Figure 1. SIS Architecture.
SIS uses simple and inexpensive alarm type sensors that can be purchased from multiple sources over EBay, Amazon.com, and other distributors. The sensors are battery operated and low power; the batteries should last for 6 months to over one year, depending upon the frequency of tripping the sensor. The sensors operate wirelessly on either the 315 MHz or the 433.92 MHz UHF bands [7]. SIS typically relies on proximity infrared (PIR) motion sensors in rooms of the residence and magnetic separation sensors on exterior doors of the residence to provide a picture of a person’s whereabouts within their home [8].
In addition to the sensors, SIS must have one “hub” device in the home. The hub is a custom built system consisting of 315 MHz and 433 MHz receivers, an advanced 32 bit microcontroller, and circuitry to communicate with the Internet via either WiFi or 3G cellular service. Software in the microcontroller:
- Decodes signals from the wireless sensors (“sensor trips”);
- Processes these signals to filter out extraneous information, reducing sensor data to relevant “events”;
- Uses a combination of time and sequenced events from more than one sensors to draw “inferences” about what is happening in the home;
- Records time-stamped events and inferences in a log (circular buffer) that is accessible via the Internet; and
- Provides a registration function for an installer to use to register sensors to the installation and designate the type and name of each sensor installed.
The processor used by the SIS [9] comes equipped with a cloud based access infrastructure. The SIS project includes a client app that is implemented as javascript-enabled web page. The client can operate on any device that has Internet access and a web browser; e.g. laptop, tablet, mobile phone, etc. The client provides both the user interface for the sensor registration function and a means to access the SIS internal log and display the log in either a graphical, timeline format or in a detailed, textual format. Examples of SIS log data from the subject’s apartment are described and analyzed in this document.
References
[1] “Caring from Afar: A Guide to Home Sensor Systems for Aging Parents”, by Richard Caro and Mary Hulme
[2] https://github.com/teampracticalprojects/SISProject
[3] There is a slow elevator ride as part of this transit, accounting for the 5 minute variability in transit time.
[4] The facility has 24 hour concierge who must open the front door manually after hours, so the subject is safe in the facility at night.
[5] As opposed to having to move her into an assisted living or memory care facility for her own safety and well being.
[6] This service is available at the subject’s facility.
[7] SIS can accommodate a mixture of 315 MHz and 433 MHz sensors in one installation.
[8] SIS can be fitted with other compatible sensors as well, including water level sensors, vibration sensors, smoke/gas alarm sensors and keyfobs.
[9] SIS uses a commercial microprocessor from Particle.io. It is compatible with both the Photon and Electron models.
*Disclosure: The research and opinions in this article are those of the author, and may or may not reflect the official views of Tech-enhanced Life.
If you use the links on this website when you buy products we write about, we may earn commissions from qualifying purchases as an Amazon Associate or other affiliate program participant. This does not affect the price you pay. We use the (modest) income to help fund our research.
In some cases, when we evaluate products and services, we ask the vendor to loan us the products we review (so we don’t need to buy them). Beyond the above, Tech-enhanced Life has no financial interest in any products or services discussed here, and this article is not sponsored by the vendor or any third party. See How we Fund our Work.